Billions of people rely on their smartphones every day for payments, authentication, and connectivity and yet the hardware foundations that make this trust possible remain largely unexamined. Trusted Execution Environments (TEEs) like ARM TrustZone and Apple’s Secure Enclave are the invisible anchors of digital security for regular consumers, protecting cryptographic keys, network credentials, provisioning and attestation processes. But while vendors assure us these enclaves are secure, there has been little independent, adversarial research to verify those claims—especially on mobile platforms.
Our project aims to close that gap. We’re launching a 9-month open research effort to rigorously study how TEEs are used in consumer mobile hardware for eSIM management and cryptographic operations.
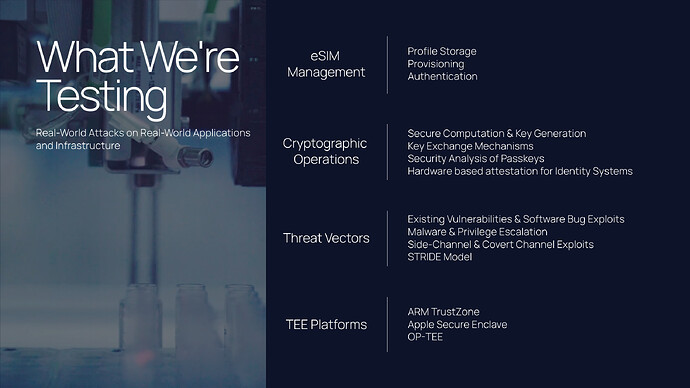
The core idea is to rigorously examine how TEEs (like ARM TrustZone and Secure Enclave) are used in consumer mobile hardware for managing eSIM credentials, provisioning processes, and cryptographic key storage. While TEEs are widely trusted in securing high-assurance workload including blockchain nodes, mobile payments, and identity verification, the specifics of how they are implemented on end-user mobile devices, especially in the context of remote SIM provisioning, remain insufficiently studied. Our project focuses on identifying these gaps, conducting low-level experiments, and surfacing any unexamined vulnerabilities that could have downstream implications on security guarantees assumed by users and application developers alike.
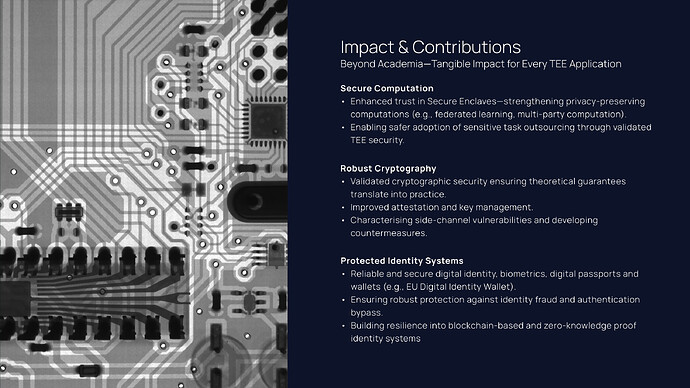
A key distinction here is that while much of TEE research has been cloud-centric or focused on generalized secure enclaves, this work anchors itself in device-native operations that mobile users rely on passively every day—eSIM profile swaps, OTA activations, carrier certificate validations, etc. We’re plan to perform targeted experiments to assess isolation boundaries, cryptographic key handling, provisioning channel security, and passkey persistence both under normal and adversarial conditions. Findings here could directly influence how secure identity or wallet apps interact with mobile TEEs, especially if hardware assumptions are misaligned with software-level trust models. This is especially relevant because of recent push by the EU to use eUICC based digital wallet identities (EUDI), this was recently put on PSE roadmap as well.
Given the shift in design goals of the web3 industry around off-chain confidential contracts and distributed TEE nodes, we believe there’s interesting common ground here and potential collaborations opportunities in examining how these lower-layer mobile trust anchors hold up—especially if mobile-native apps begin to interface with chain-anchored attestation mechanisms or rely on secure key generation at the edge. If TEEs on mobile devices can be evaluated for cryptographic integrity and provisioning robustness under common adversarial models, it may serve as a foundational check for any privacy-preserving protocol that extends into the consumer mobile domain.
The project is structured with open access in mind. All experiments, codebases, and resulting documentation will be published under free-use open-source licenses. The primary objective is to build shared knowledge and tooling that can be reused across efforts in the broader TEE and privacy-tech ecosystems. We’ve budgeted this as a 9-month focused study with detailed milestones and hardware-in-the-loop evaluations.
We would be happy to answer any specific questions and explore if there’s any overlap in interest areas or technical steps where collaboration or feedback exchange could add value on both ends. We’re also looking for research grants for this work so any help in that area would also be greatly appreciated!
Here is the pitch deck and the full proposal -
Pitch Deck
Full Proposal